The Narrative Escalation of a Healthcare Ransomware Breach examines how a technical cybersecurity vulnerability evolved into a full-scale institutional crisis narrative.
The report analyzes the exploitation of a critical flaw in BeyondTrust remote-access software and the resulting ransomware incident affecting the University of Mississippi Medical Center.
The case illustrates how modern cyber incidents unfold across two distinct narrative tracks. The first emerges within specialized cybersecurity communities as vulnerabilities are disclosed, exploitation risks are analyzed, and patch advisories circulate among security professionals. The second begins once operational disruption becomes public, shifting coverage toward institutional impact, healthcare service interruptions, and broader concerns about cybersecurity resilience.
Together, these narratives demonstrate how vulnerability disclosures can rapidly escalate into operational, reputational, and strategic challenges for organizations in critical sectors such as healthcare.
This report examines the exploitation of a critical vulnerability in BeyondTrust remote-access software and the disruption that followed at the University of Mississippi Medical Center (UMMC). By analyzing open-source reporting, incident timelines, and narrative coverage surrounding the breach, the report illustrates how software vulnerabilities can escalate rapidly into enterprise-wide security crises.
The findings also demonstrate how early reporting in specialized cybersecurity media can provide valuable warning signals before operational disruption occurs. Monitoring these signals can allow organizations to prioritize remediation efforts, strengthen incident preparedness, and reduce exposure to ransomware campaigns targeting privileged-access platforms.
This case study highlights a broader trend in modern cyber incidents: Vulnerabilities often emerge first within technical reporting ecosystems, but their consequences eventually spread into institutional and public narratives once real-world disruption occurs.
1. Cybersecurity media provided early warning signals.
Initial reporting appeared approximately ten days before the breach became public.
2. Trusted cybersecurity publications drove the initial narrative.
Sources such as Bleeping Computer, SecurityWeek, and The Hacker News provided reliable technical reporting focused on vulnerability disclosure and remediation.
3. Narrative escalation followed a predictable trajectory.
Technical vulnerability reporting evolved into operational disruption and national media coverage once healthcare systems were affected.
Vulnerabilities often emerge first within technical reporting ecosystems, but their consequences eventually spread into institutional and public narratives once real-world disruption occurs.
Ransomware activity continues to evolve rapidly, with attackers increasingly exploiting software vulnerabilities to gain privileged access to enterprise systems. One of the most significant recent threats involves a critical flaw in BeyondTrust remote-access products.
The vulnerability, tracked as CVE-2026-1731, affects BeyondTrust Remote Support and Privileged Remote Access software and carries a near-maximum severity score of CVSS 9.9. It allows attackers to execute operating-system commands remotely without authentication, meaning that no credentials or user interaction are required to compromise a vulnerable system.
Modern ransomware groups increasingly target identity platforms, remote-management tools, and supply-chain software because these systems provide immediate high-level access to enterprise environments.
Because BeyondTrust tools are widely used across government agencies, healthcare organizations, and private enterprises, exploitation of this vulnerability poses significant operational and economic risks. Successful cyberattacks leveraging such flaws can:
The vulnerability also carries broader national-security implications. Privileged-access systems are commonly deployed within federal agencies and critical infrastructure networks. If left unpatched, such systems could potentially be exploited to penetrate sensitive government networks or disrupt essential digital services.
Security researchers and government agencies have confirmed that the BeyondTrust flaw has already been exploited in the wild. Threat actors have used it to deploy web shells, establish command-and-control channels, move laterally across networks, and steal sensitive data as part of ransomware campaigns.
Modern ransomware groups increasingly target identity platforms, remote-management tools, and supply-chain software because these systems provide immediate high-level access to enterprise environments. Once attackers gain privileged access, they often combine data theft with extortion tactics, threatening to release stolen information if victims refuse to pay.
The narrative surrounding the BeyondTrust remote support vulnerability developed rapidly across specialized cybersecurity media before the breach at the University of Mississippi Medical Center (UMMC) became public. Monitoring these early signals reveals how vulnerability disclosures move from technical reporting to operational and institutional risk.
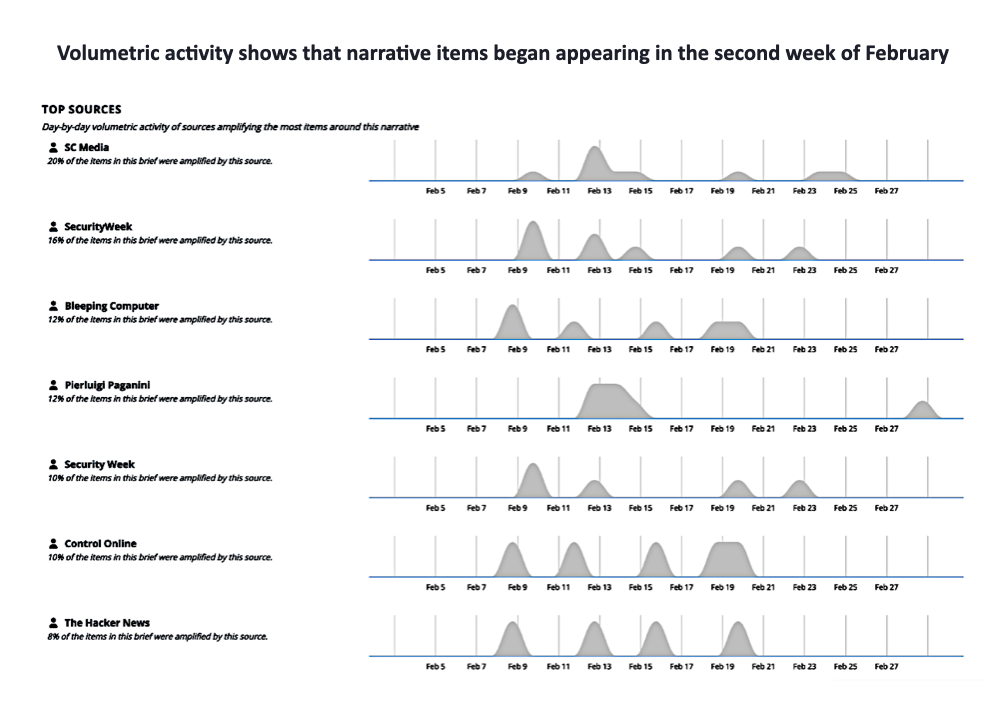
The first wave of reporting emerged in early February within highly specialized cybersecurity outlets. Publications such as Bleeping Computer, The Hacker News, SecurityWeek, Rapid7, and Help Net Security began reporting on a critical remote code execution (RCE) vulnerability affecting BeyondTrust remote support systems.
Early headlines focused on the technical nature of the flaw and the urgency of patching affected systems. Coverage warned that the vulnerability could allow attackers to gain unauthorized access, execute commands remotely, and potentially exfiltrate sensitive data from compromised environments.

Examples of early reporting included:
At this stage, the narrative remained largely technical and confined to cybersecurity audiences. However, the language of the reporting quickly escalated from vulnerability disclosure to warnings of active exploitation.
Within days of the initial reporting, cybersecurity researchers began identifying signs that the vulnerability was being actively exploited.
Coverage shifted from describing the flaw to warning that attackers were using the vulnerability to deploy web shells, establish backdoors, and extract data from affected systems.
Coverage shifted from describing the flaw to warning that attackers were using the vulnerability to deploy web shells, establish backdoors, and extract data from affected systems. Headlines increasingly emphasized phrases such as “actively exploited,” “ransomware attacks,” and “data exfiltration.”
This transition marked a critical shift in the narrative trajectory. What began as a technical vulnerability disclosure became a broader security alert across the cybersecurity ecosystem.
The amplification patterns within cybersecurity media reflect this escalation. Articles began referencing each other’s reporting and citing research from threat intelligence groups such as Rapid7, while technical blogs and cybersecurity analysts amplified the warnings across social channels.
The narrative reached a new phase when the U.S. Cybersecurity and Infrastructure Security Agency (CISA) formally recognized the severity of the vulnerability.
CISA added the BeyondTrust flaw to its Known Exploited Vulnerabilities catalog and issued directives requiring federal agencies to patch affected systems within a defined timeframe. This government action significantly amplified the narrative beyond the cybersecurity research community.
At this stage, the issue was no longer framed solely as a technical vulnerability. Instead, it became a recognized national cybersecurity risk requiring coordinated remediation across government networks.
The progression from vulnerability disclosure to federal patch directives demonstrates how cybersecurity narratives evolve through distinct stages of escalation.

The reporting patterns reveal a clear narrative progression:
This trajectory illustrates how specialized cybersecurity reporting can serve as an early indicator of emerging operational risk.
In the case of the BeyondTrust vulnerability, initial reporting appeared in cybersecurity media on February 9—approximately ten days before the breach at UMMC disrupted hospital operations.
Looking at the pattern in the chart:
The University of Mississippi Medical Center detected the breach during the early hours of February 19, triggering widespread disruption across its network.
The attack affected multiple IT systems, including the EPIC electronic medical record system, as well as telephone and email access. As a result, healthcare services were temporarily suspended across 35 clinics throughout the state.

UMMC coordinated its response with federal authorities, including the Department of Homeland Security and the FBI.
News of the breach quickly spread across national media outlets. Within a day of the announcement, coverage appeared in major cities across the United States, including Los Angeles, Boston, Dallas, and Boulder.
The EdgeScout Narrative Search platform tracked approximately 25 narrative items related to the incident between February 20 and February 26, after which reporting activity subsided.
Although national coverage of a cybersecurity breach is common, it can introduce additional challenges for affected organizations. Media attention may lead to perceptions of inadequate cybersecurity practices or systemic negligence.
Patients and partners may also become concerned about the reliability of healthcare services following a cyberattack.
The BeyondTrust incident illustrates how cyber crises often evolve through two interconnected narrative trajectories.
The first narrative developed within specialized cybersecurity media following the disclosure of the vulnerability.
This narrative focused on:
The audience consisted primarily of cybersecurity professionals, system administrators, and threat-intelligence analysts.
Typical of this approach was an item published by Bleeping Computer on February 9th. It detailed the discovery of the flaw, the versions of BeyondTrust that were impacted, and the steps needed to repair it. CSO Online took much the same route, though it did warn that "around 11,000 instances of BeyondTrust Remote Support are currently exposed to the internet and estimated that around 8,500 of those are on-premises deployments that need patching."

Narrative item published by Bleeping Computer, Feb. 9, 2026
A second narrative emerged once the vulnerability translated into operational disruption at UMMC.
Media coverage shifted toward:
At this stage, the narrative moved beyond cybersecurity communities and entered mainstream public discourse.
With this shift, a new emphasis entered the coverage. While technical publications continued to focus on the flaw itself, broader media outlets concentrated their energies towards disclosing the attack and detailing its impact on the broader public. The Clarion-Ledger, for example, made mention of the fact that all 35 UMMC clinics were forced to suspend operations. It also noted that "Administrative functions, such as billing and the hospital's websites, are also affected. UMMC's phone system is also compromised, with many hospital and clinical numbers unable to take calls." Missing from its coverage was any description of the security flaw, how it is exploited, or how it is repaired. As the audience shifted, so did the narrative.

Narrative item published by the Clarion Ledger, Feb. 25th, 2026
A major consequence of this narrative activity is the reputational damage it can cause for affected organizations. This is the case even when the coverage does not use overtly accusatory language. Merely describing the impact of a breach may be sufficient to create public doubts about both an organization's security posture and the securityware it uses to maintain it.
With regard to BeyondTrust, the coverage largely strove to maintain a neutral tone. Yet in explaining the vulnerabilities found in the software, these outlets necessarily made observations that could potentially undermine BeyondTrust's public reputation. Bleeping Computer, in describing the flaw's ease of use, noted that "threat actors with no (login) privileges can exploit it in low-complexity attacks that don't require user interaction" Meanwhile, The Hacker News informed audiences that ransomware attempts were being made against "financial services, legal services, high technology, higher education, wholesale and retail, and healthcare sectors across the U.S., France, Germany, Australia, and Canada."

Narrative item published by The Hacker News, Feb. 20, 2026
Customers and partners often expect security products to meet a higher standard of reliability, so the disclosure of a vulnerability and its wide-scale exploitation may raise doubts about the company’s development practices, code auditing, and internal security controls. Media coverage and industry discussion can amplify these concerns, creating perceptions that the vendor failed to anticipate or prevent serious risks. Even if the company responds quickly with a patch, the incident can erode trust among existing clients, slow new sales, and invite closer scrutiny from regulators, auditors, and cybersecurity researchers. Over time, repeated vulnerabilities can lead stakeholders to question the vendor’s overall competence and reliability in safeguarding critical systems.
But the coverage also brought reputational risks for UMMC, as well. While local and national news reports generally steered clear of accusatory language, they nonetheless went to great lengths to describe the impact of the breach, paying special attention to the consequences for both caregivers and patients. One outlet, the Mississippi Free Press, noted that the "attack has affected the provider’s access to its electronic medical records system, Epic, leaving doctors unable to access patient health information necessary for normal operations." Local TV channel WAPT used the breach as a springboard reporting the broader issue that "Mississippi lacks statewide hospital cybersecurity standards."

Narrative item published by WAPT, Feb. 20, 2026
When a health system suffers a ransomware attack, the resulting publicity can significantly affect its reputation. Patients, partners, and regulators may question the organization’s ability to safeguard sensitive medical and personal data, particularly because healthcare institutions are expected to maintain strong privacy protections. Media coverage of the incident can amplify concerns about medical identity theft, exposure of personal health information, and disruptions to clinical services such as appointments, prescriptions, or electronic medical records. Even if the attack is quickly contained, the perception of weakened cybersecurity can erode patient confidence, strain relationships with insurers and partner hospitals, and trigger additional scrutiny from regulators. Over time, this loss of trust may lead to reduced patient engagement, reputational harm within the healthcare community, and increased pressure to demonstrate stronger cybersecurity practices.
The BeyondTrust case demonstrates how monitoring trusted cybersecurity reporting can provide early warning signals before operational disruption occurs.
Cyber incidents increasingly generate two distinct narrative tracks. The first develops within technical cybersecurity media as vulnerabilities are disclosed and exploitation warnings emerge. The second begins once breaches occur, shifting coverage toward institutional disruption and reputational consequences.
Cyber incidents increasingly generate two distinct narrative tracks. The first develops within technical cybersecurity media as vulnerabilities are disclosed and exploitation warnings emerge. The second begins once breaches occur, shifting coverage toward institutional disruption and reputational consequences.
Organizations capable of identifying these early signals gain valuable time to prioritize patching, prepare communications strategies, and reduce both operational and reputational risk.
The exploitation of the BeyondTrust vulnerability illustrates how quickly a single software flaw can escalate into a large-scale operational crisis.
As ransomware groups increasingly target privileged-access and remote-management platforms, organizations must treat vulnerability monitoring, patch management, and incident preparedness as strategic priorities.
The disruption experienced by the University of Mississippi Medical Center demonstrates the real-world consequences when such vulnerabilities are exploited in critical sectors like healthcare.
Organizations that combine proactive threat intelligence, rapid patch deployment, and narrative monitoring will be better positioned to detect emerging cyber risks and mitigate their impact before incidents escalate into institutional crises.